Imagine handing the keys to a bank vault to anyone who walks by. That is essentially what happens when a smart contract has broken access control. In the world of blockchain, code is law, but only if that code knows who is allowed to execute it. Access control vulnerabilities are not just theoretical risks; they are the leading cause of massive financial losses in decentralized finance (DeFi). When permission checks fail, attackers can drain funds, pause protocols, or rewrite the rules of the game entirely.
The stakes have never been higher. With the global blockchain security market projected to reach $67.34 billion by 2026, understanding these flaws is no longer optional for developers-it is survival. This article breaks down exactly how these vulnerabilities work, why they happen, and how you can lock your contracts down before an exploit takes place.
What Are Access Control Vulnerabilities?
At its core, an access control vulnerability occurs when a smart contract fails to verify if the person calling a function has the right to do so. Think of it like a house with a front door that looks locked but opens for anyone who pushes it hard enough. In smart contracts, this usually means missing or flawed checks on sensitive functions.
These vulnerabilities allow unauthorized parties to:
- Execute administrative operations, such as upgrading the contract logic.
- Manipulate the contract state, like changing token balances or pausing transfers.
- Drain funds directly from the contract’s wallet.
According to the OWASP Smart Contract Top 10, access control issues are consistently among the most critical risks. They account for approximately 25-30% of all vulnerabilities found during professional audits. The problem isn't always complex math errors; often, it is simply forgetting to ask "Who are you?" before letting someone change the settings.
Common Types of Access Control Flaws
Not all access control failures look the same. Static analysis tools like AChecker identifies five primary ways these checks break down.
- Missing Checks on Critical Instructions: The most basic error. A developer writes a function to update the owner address but forgets to add a
require(msg.sender == owner)check. Anyone can call it. - Bypassing Modifiers: Developers sometimes create custom modifiers with confusing names. If the modifier name doesn't clearly indicate it restricts access, other team members might skip using it, assuming the function is public-safe.
- Direct Manipulation of State Variables: Attackers find ways to alter the variables that store permissions (like role flags) without going through the proper authorization process.
- Taint Flows: Malicious data enters the contract through a seemingly safe function and influences a decision made later in a restricted function, bypassing the intended logic.
- Incorrect Naming Conventions: Using private visibility for internal functions that are still callable via low-level calls, allowing attackers to invoke them indirectly.
The complexity here lies in intent. Sometimes, developers intentionally leave certain variables mutable under specific constraints. Distinguishing between a feature and a flaw requires deep context, which is why automated tools often produce false positives.
Real-World Disasters: Lessons from History
Theory is one thing; losing millions is another. Two major incidents shaped the current landscape of smart contract security.
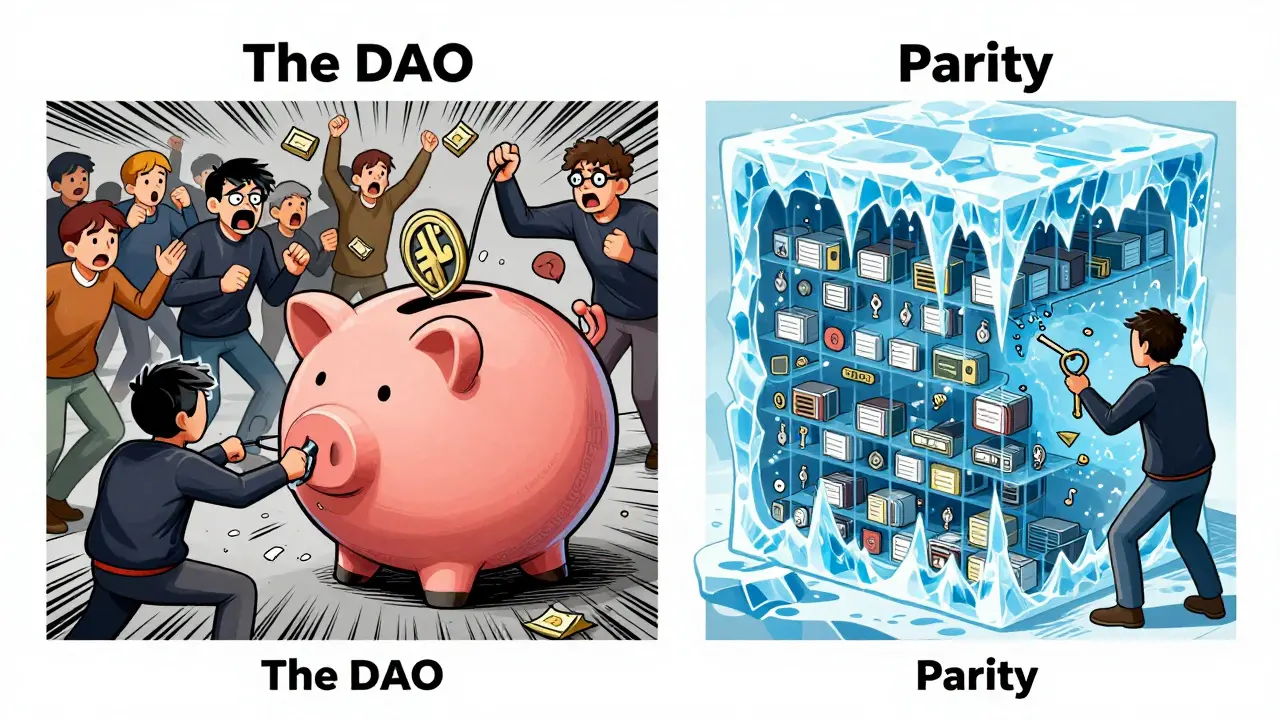
The DAO Hack (2016)
This is the most infamous case in Ethereum history. The DAO was a decentralized autonomous organization holding over $150 million in funds. An attacker exploited a flaw in the access control logic related to recursive calls. By repeatedly calling a split function before the balance was updated, the attacker drained more than $50 million. This event was so catastrophic it led to a controversial hard fork of the Ethereum network to reverse the theft.
The Parity Multisig Hack (2017)
Parity provided a popular multisignature wallet contract. The issue wasn't a lack of access control, but rather a bug in how ownership was initialized. Because the library contract was deployed incorrectly, anyone could claim ownership of the library itself. This allowed an attacker to freeze the library, locking over $280 million across thousands of wallets. It highlighted that even sophisticated RBAC systems can fail if the underlying initialization logic is flawed.
Implementing Secure Access Control
You don't need to reinvent the wheel. In fact, trying to write your own access control logic from scratch is one of the biggest risks you can take. The industry standard is to use battle-tested libraries.
OpenZeppelin Contracts
OpenZeppelin provides the most widely used implementation for secure access control. As of 2026, about 68% of smart contract developers utilize their frameworks, up from just 23% in 2019. Their Ownable and AccessControl contracts handle the heavy lifting.
Here is how a basic secure implementation looks:
import "@openzeppelin/contracts/access/Ownable.sol";
contract MyToken is Ownable {
// Only the owner can mint tokens
function mint(address to, uint256 amount) public onlyOwner {
_mint(to, amount);
}
}The onlyOwner modifier ensures that msg.sender matches the contract's owner address. If it doesn't, the transaction reverts immediately.
Advanced Mitigation Strategies
Simple ownership isn't enough for complex DeFi protocols. You need layered security.
- Role-Based Access Control (RBAC): Instead of one owner, define roles like
MINTER_ROLE,AUDITOR_ROLE, andEMERGENCY_PAUSE_ROLE. This follows the principle of least privilege-users get only the permissions they absolutely need. - Multisignature Wallets: Require multiple signatures (e.g., 3 out of 5) to execute critical actions. This prevents a single compromised key from destroying the contract.
- Timelocks: Add a delay between deciding to upgrade a contract and actually executing the upgrade. This gives users time to withdraw their funds if they notice malicious changes.
- Modular Design: Separate your access control logic from your business logic. This makes auditing easier because security experts can focus purely on permission checks without getting distracted by tokenomics.

Detection Tools and Auditing
How do you find these bugs before hackers do? You combine automated tools with human expertise.
Static Analysis: Tools like AChecker perform information-flow analysis to detect missed checks. However, be aware that these tools struggle with non-standard patterns. They are great for catching obvious mistakes but poor at understanding nuanced business logic.
Professional Audits: For any project handling real money, a manual audit is non-negotiable. Firms like Trail of Bits, ConsenSys Diligence, and OpenZeppelin offer specialized assessments. Expect to pay between $5,000 and $50,000 depending on complexity, with turnaround times of 2-4 weeks. Projects with robust access controls score 15-20% higher on security assessments according to DeFiSafety reports.
Formal Verification: This is the gold standard. Using tools like the K Framework or Dafny, you can mathematically prove that your access control logic is correct under all possible conditions. While expensive and complex, it eliminates entire classes of bugs.
Future Trends in Access Control
The landscape is evolving rapidly. Zero-knowledge proofs (ZKPs) are being explored to create privacy-preserving access controls, where permissions are verified without revealing user identities. Layer 2 scaling solutions introduce new challenges, requiring cross-chain permission verification to ensure a user authorized on one chain is recognized on another.
Additionally, AI-driven static analysis tools are improving their accuracy, reducing false positives and helping developers spot subtle taint flows faster. Regulatory bodies are also beginning to mandate formal security assessments for high-value smart contracts, making comprehensive access control auditing a legal requirement in some jurisdictions.
| Mechanism | Security Level | Complexity | Best Use Case |
|---|---|---|---|
| Single Owner | Low | Low | Simple dApps, Prototypes |
| RBAC | Medium | Medium | Standard DeFi Protocols |
| Multisig + Timelock | High | High | Large Treasury Management |
| Formal Verification | Highest | Very High | Critical Infrastructure, Banking |
What is the most common access control vulnerability?
The most common vulnerability is missing function guards. This happens when developers forget to add require statements or modifiers that check if the caller is authorized. It allows any external account to trigger administrative functions.
Is using OpenZeppelin enough to prevent hacks?
Using OpenZeppelin significantly reduces risk, but it is not a silver bullet. Misconfiguration, such as setting the wrong initial owner or failing to implement role-based restrictions correctly, can still lead to exploits. Always pair library usage with professional audits.
How much does a smart contract audit cost?
Costs vary based on complexity, but typically range from $5,000 to $50,000. Simple contracts may be on the lower end, while complex DeFi protocols with multiple interacting contracts will be on the higher end. Turnaround time is usually 2-4 weeks.
What is the difference between Ownable and RBAC?
Ownable grants full control to a single address. RBAC (Role-Based Access Control) allows you to define multiple roles with specific permissions. RBAC is safer for larger teams because it distributes trust and limits the damage if one key is compromised.
Can automated tools find all access control bugs?
No. Automated tools like AChecker are excellent for finding syntax errors and missing checks, but they cannot understand business logic. They often miss subtle logical flaws or intentional design choices that become vulnerabilities in edge cases. Human auditors are essential.
Why did the Parity Multisig hack happen?
It happened due to improper initialization. Users instantiated the library contract instead of inheriting it, allowing an attacker to claim ownership of the shared library code. This froze all wallets relying on that library, demonstrating the danger of shared code dependencies.
What is a timelock in smart contracts?
A timelock is a mechanism that delays the execution of a transaction for a set period (e.g., 48 hours). It gives users time to react and withdraw funds if they suspect an admin is planning a malicious upgrade or action.
How does gas limit affect access control?
Complex access control logic consumes more gas. If a check is too expensive, it can make transactions unaffordable for users or potentially be exploited in denial-of-service attacks. Efficient coding practices are crucial to keep costs low while maintaining security.
Categories
Popular Articles